Many Stockholm businesses believe a simple password makes their WiFi network secure. In reality, proper wireless protection goes much deeper, covering every device and connection, from access points to switches. Misunderstanding WiFi security leaves your company exposed to avoidable risks and costly breaches. This guide brings clarity to common myths and outlines robust strategies for small and medium enterprises that want reliable and secure wireless networks with Ubiquiti Unifi.
Table of Contents
- Defining Secure WiFi and Its Misconceptions
- What Secure WiFi Actually Means
- Why This Matters to Your Business
- Types of Secure Wireless Network Protocols
- WPA2: Still Widely Used, But Showing Its Age
- WPA3: The Current Standard
- Which Protocol Should Your Business Use?
- Essential Features of Ubiquiti Unifi Security
- Centralised Security Management
- The UniFi Security Gateway
- UniFi CyberSecure: Advanced Threat Protection
- Network Segmentation and Access Control
- Professional Installation and Network Cabling
- Risks of Poor WiFi Security and Solutions
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive Security Management | Secure WiFi requires ongoing management, regular updates, and adherence to current encryption standards like WPA3. |
| Myths About Network Security | Many SMEs operate under misconceptions, believing hidden networks or outdated encryption methods are sufficient protection. |
| Risk Assessment and Segmentation | Effective security involves network segmentation and restriction of access to sensitive systems to mitigate risks of breaches. |
| Professional Installation Importance | Quality cabling and professional installation significantly enhance network performance and reliability, preventing future issues. |
Defining Secure WiFi and Its Misconceptions
WiFi security means far more than just setting a password. It encompasses protecting every component of your wireless network—from access points and switches to client devices—throughout the entire lifecycle of your system.
Many small and medium enterprises in Stockholm operate under dangerous assumptions about their wireless networks. The most common mistake? Believing that because something is wireless, it is somehow inherently secure.
Common WiFi Security Misconceptions
Here’s what business owners and IT managers often get wrong:
-
“My network is hidden, so it’s safe.” Hiding your network name (SSID) provides zero real security. Attackers detect hidden networks just as easily as visible ones.
-
“WEP or WPA encryption is enough.” Outdated encryption standards like WEP are completely broken. Even older WPA implementations have known vulnerabilities that criminals actively exploit.
-
“I don’t need to update my access point firmware.” This is particularly risky. Firmware updates patch critical security holes. Skipping them leaves your network wide open.
-
“Wireless networks are inherently risky, so I’ll just avoid them.” Wrong approach. Modern standards like WPA3 provide excellent security when properly configured.
-
“My switch and router don’t need security focus.” NIST wireless security guidance emphasises that you must secure all WLAN components, not just access points. Your wired infrastructure is equally critical.
What Secure WiFi Actually Means
Secure WiFi requires active management and proper configuration. It is not a feature you enable once and forget about.
True wireless security includes:
- Current encryption standards (WPA3 or WPA2 at minimum)
- Regular firmware updates on all devices
- Strong authentication protocols
- Network segmentation using VLANs
- Continuous monitoring and maintenance
- Client device oversight
According to best practices for wireless network security, unsecured wireless networks allow cybercriminals direct access to sensitive business information. Yet many SMEs treat WiFi as secondary infrastructure.
Why This Matters to Your Business
An unsecured WiFi network is essentially an open door to your company data. Customer information, financial records, employee credentials—all accessible to anyone sitting in your car park with a laptop.
Proper WiFi security protects your reputation, avoids regulatory fines, and keeps operational systems stable. It also reduces the risk of ransomware infections that spread through unprotected wireless access.
Pro tip: Start by auditing your current setup: What encryption standard are you using? When was the last firmware update? Are different user types (employees, guests, contractors) on separate networks? These answers reveal whether your security is truly robust or just appearing to be.
Types of Secure Wireless Network Protocols
Wireless security protocols form the foundation of any protected network. These standards encrypt data travelling across your WiFi and authenticate users accessing your system. Understanding the differences between them helps you make informed decisions about your SME’s network infrastructure.
The wireless security landscape has evolved significantly. Older protocols proved vulnerable to attack, which is why modern standards exist—and why you should avoid anything outdated.
The Evolution of Wireless Security
Wireless networks have progressed through several generations of security standards:
To better understand the progression of wireless security, here is a comparison of protocol strengths and weaknesses:
| Protocol | Year Introduced | Main Strength | Major Weakness |
|---|---|---|---|
| WEP | 1997 | Simple setup | Easily hacked in minutes |
| WPA | 2003 | Improved over WEP | Still exploited by attackers |
| WPA2 | 2004 | Reliable AES encryption | Vulnerable to password attacks |
| WPA3 | 2018 | Robust authentication, strong protection | Limited by device compatibility |
-
WEP (Wired Equivalent Privacy) – The original standard from the 1990s. Now completely broken and exploitable in minutes.
-
WPA (WiFi Protected Access) – Introduced around 2003 to fix WEP’s critical flaws. Better, but still considered outdated today.
-
WPA2 (WiFi Protected Access 2) – Arrived in 2004 with stronger encryption using AES. This became the industry standard for nearly two decades.
-
WPA3 (WiFi Protected Access 3) – The current standard, released in 2018. Adds enhanced protections that WPA2 lacks.
WPA2: Still Widely Used, But Showing Its Age
WPA2 remains acceptable for most SME deployments. It uses AES encryption, which is mathematically solid and difficult to crack with current technology.
However, WPA2 has known limitations:
- Vulnerable to brute force attacks on weak passwords
- KRACK attacks can exploit certain implementations
- No protection against dictionary attacks on pre-shared keys
Thousands of Stockholm businesses still run WPA2 successfully. The protocol is not insecure—it simply lacks modern protections.
WPA3: The Current Standard
WPA3 introduces individualized data encryption and significantly improved authentication mechanisms. It protects against brute force attacks even with weak passwords.
Key WPA3 advantages:
- Simultaneous Authentication of Equals (SAE) – Replaces the older Pre-Shared Key method with stronger cryptography
- Opportunistic Wireless Encryption (OWE) – Encrypts data on open networks without requiring a password
- Protection from password guessing attacks – Even if an attacker captures your network traffic
- Better protection for IoT devices – Simplified onboarding without compromising security
WPA3 is now the recommended standard for all new network deployments. If you’re installing a network today, this is what you should choose.
Which Protocol Should Your Business Use?
For most SMEs in Stockholm, the answer depends on your equipment and timeline. Ubiquiti Unifi access points support both WPA2 and WPA3, giving you flexibility.
If your devices support WPA3, deploy it immediately. If you’re stuck with older client devices that only support WPA2, that remains acceptable—but plan to upgrade as equipment ages.
According to IEEE 802.11 wireless standards and security protocols, the security strength of any protocol depends heavily on proper configuration and regular maintenance, not just the standard itself.
Pro tip: Check your current Unifi controller settings now. Most access points default to WPA2 or allow mixed WPA2/WPA3 mode. If you have business-critical data, test whether your client devices (laptops, phones, printers) support WPA3 before switching—upgrading improves security without disrupting operations.
Essential Features of Ubiquiti Unifi Security
Ubiquiti Unifi delivers security capabilities specifically designed for businesses that need reliable, manageable protection without enterprise complexity. The system centralises security controls, giving your IT team visibility and command over the entire network from one dashboard.
Unlike consumer WiFi routers, Unifi security integrates across access points, gateways, and switches. This unified approach means threats are caught at multiple points rather than relying on a single defence layer.
Centralised Security Management
The Unifi Controller dashboard is where all security happens. You configure firewall rules, monitor threats, and adjust policies without visiting individual devices.
This centralised approach delivers:
- Single interface for managing multiple access points and gateways
- Real-time visibility into network traffic and connected devices
- Rapid policy deployment across your entire infrastructure
- Detailed logging of all security events for compliance and troubleshooting
Many Stockholm SMEs struggle with fragmented security tools. Unifi eliminates that headache by consolidating controls into one platform.
Here is a summary of key Ubiquiti Unifi security functions and their impact on SME network safety:
| Security Feature | What It Does | Business Benefit |
|---|---|---|
| Centralised control | Unified dashboard for all devices | Reduces complexity, speeds response |
| Intrusion detection | Real-time threat monitoring | Blocks attacks before causing harm |
| Traffic shaping | Prioritises business-critical apps | Improves performance and reliability |
| VLAN segmentation | Separate user and IoT networks | Limits attacker movement, protects assets |
The UniFi Security Gateway
The UniFi Security Gateway provides firewall and routing capabilities with traffic management and intrusion detection built in. It sits between your internet connection and internal network, filtering threats before they reach your devices.
Key gateway security features:
- Advanced firewall rules – Block traffic by IP, port, protocol, or content type
- Intrusion detection and prevention – Automatically block suspicious traffic patterns
- Traffic shaping – Prioritise critical business applications
- VPN capabilities – Secure remote access for employees working from home
- Deep packet inspection – Analyse traffic content, not just headers
The gateway is your first line of defence. Every network connection passes through it, making it the ideal place to catch threats early.
UniFi CyberSecure: Advanced Threat Protection
For businesses handling sensitive data, UniFi CyberSecure takes protection further. This subscription service integrates Ubiquiti hardware with Proofpoint threat intelligence, scanning web traffic in real time.
CyberSecure blocks:
- Malware and ransomware before installation
- Phishing websites and credential-stealing attacks
- Botnet command-and-control communications
- Suspicious file downloads and exploits
- Zero-day threats using behavioural analysis
Your users can browse normally whilst advanced threat blocking protects against phishing and malware. The service works invisibly in the background.
Network Segmentation and Access Control
Unifi lets you create separate networks for different user groups. Employees, guests, contractors, and IoT devices can all operate on isolated networks with different security rules.
This segmentation prevents lateral movement if one segment is compromised. An attacker gaining access to a guest network cannot reach your financial systems.
Why This Matters for Your Business
Security that’s difficult to manage often goes neglected. Unifi’s integrated approach makes security part of your daily workflow rather than a separate headache.
Pro tip: Start by enabling the UniFi Security Gateway’s intrusion detection and reviewing firewall logs weekly. Most SMEs leave default settings untouched—spending one afternoon customising rules for your specific traffic patterns catches issues before they become breaches.
Professional Installation and Network Cabling
Proper network cabling forms the backbone of reliable WiFi performance. Even the best Ubiquiti Unifi access points deliver poor results if the underlying infrastructure is poorly designed or installed.
Most SMEs underestimate how much cabling quality affects overall network reliability. Bad installations create bottlenecks, signal interference, and frequent disconnections that frustrate users and damage productivity.
Why Professional Installation Matters
Installation quality directly impacts network uptime and performance. A poorly installed cable might work initially but degrade over months as connectors loosen or moisture enters connections.
Professional installation protects your investment:
- Reduces costly downtime from cable failures
- Ensures optimal data transfer speeds
- Simplifies future maintenance and upgrades
- Meets compliance requirements for business-critical systems
- Extends equipment lifespan by 30-50%
Stockholm businesses often discover cabling problems only after networks start failing. Prevention costs far less than emergency repairs.
Standards-Based Installation Practices
BICSI installation standards provide comprehensive guidance on telecommunications cabling best practices. These cover planning, quality assurance, documentation, and ongoing maintenance to ensure reliable installations suited for SME networks.
Key installation considerations:
- Cable type selection – Cat6A or Cat7 for future-proofing beyond basic Cat6
- Proper routing – Avoiding interference from electrical cables and HVAC systems
- Connector termination – Precise specifications preventing signal loss
- Testing and certification – Verifying performance before handing over the system
- Documentation – Detailed labelling and records for troubleshooting
Professional installation isn’t just about getting cables in the walls. It’s about building infrastructure that stays reliable for 10+ years.
Cable Management and Infrastructure
Organised cabling simplifies troubleshooting and reduces future costs. When technicians can identify cables quickly, they resolve problems faster.
Proper cable management includes:
- Colour-coded labelling at both ends
- Cable runs separated from electrical power
- Sufficient slack for future relocations
- Proper support avoiding strain on connections
- Organised patch panels in central locations
Undocumented installations become nightmares when problems occur. You’ll spend hours tracing unlabelled cables instead of minutes fixing the issue.
Testing and Certification
ISO/IEC 14763-2 standards require testing and inspection to ensure proper installation practices. Professional installers certify that cables meet performance specifications before you depend on them.
Testing verifies:
- Signal integrity across all frequencies
- Impedance matching
- Absence of crosstalk
- Proper grounding
- Physical cable integrity
Certification documents become critical if you need to claim warranty coverage later.
Integrating Cabling with Ubiquiti Unifi
Your cabling must support your access point density and switch capabilities. High-performance Unifi equipment connected through inadequate cabling is like installing a sports car engine in a standard car frame.
Pro tip: When planning your installation, specify Cat6A minimum even if Cat6 seems sufficient today. The slight additional cost prevents future bottlenecks as your business adds users and bandwidth-intensive applications—and professional installers can often run Cat6A for only marginally more than Cat6.
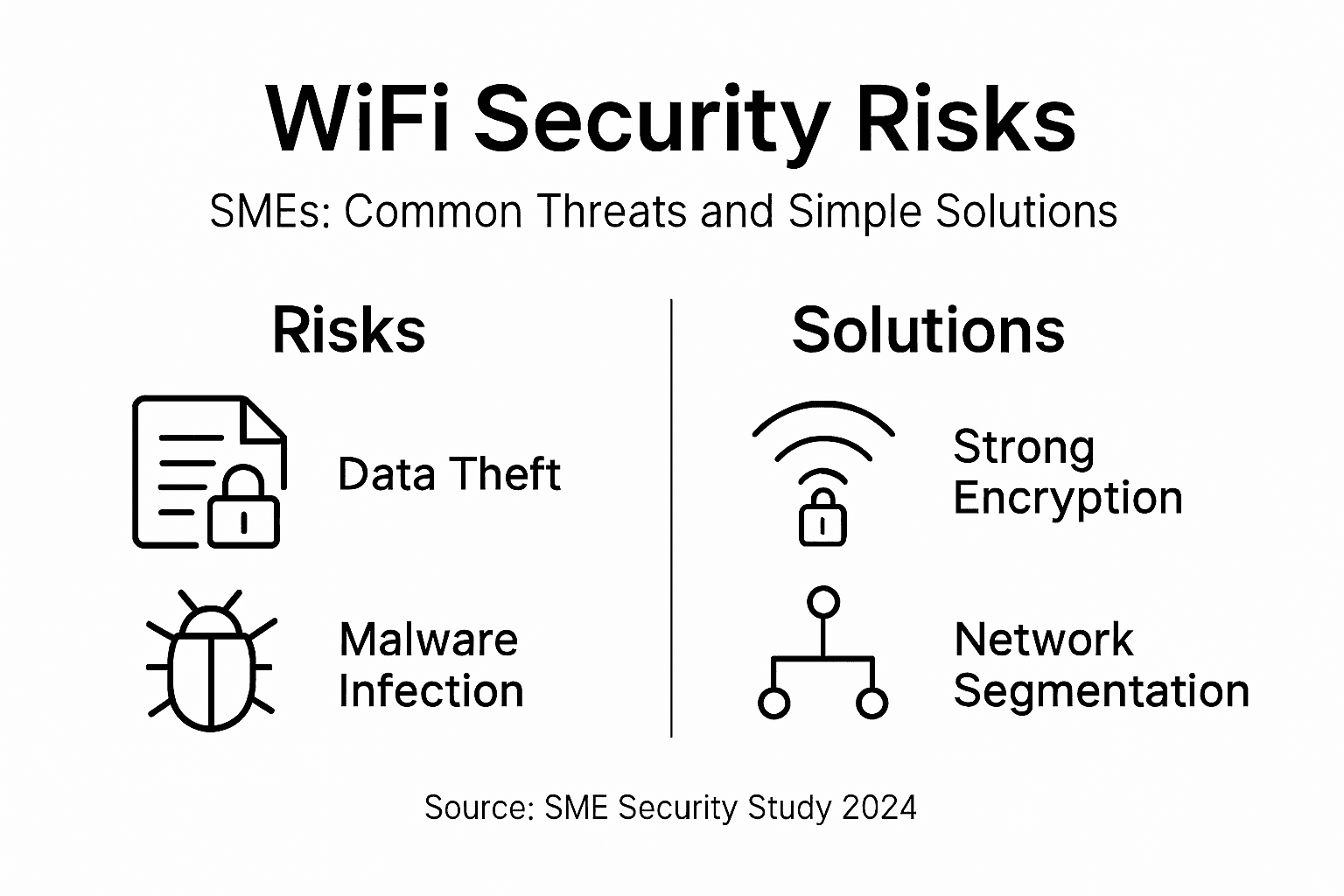
Risks of Poor WiFi Security and Solutions
Unsecured WiFi networks are open invitations to cybercriminals. They gain access to sensitive business data, financial records, customer information, and intellectual property without your knowledge.
Many SME owners believe their networks are too small to attract attackers. This is dangerously wrong. Criminals target small businesses precisely because security is often weaker than at larger enterprises.
The Real Business Impact
Poor WiFi security creates measurable financial damage. Data breaches cost businesses thousands in recovery, notification, potential fines, and reputational harm.
Common consequences include:
- Identity theft affecting customers and employees
- Ransomware infections halting operations entirely
- Malware stealing intellectual property or financial data
- Regulatory fines under GDPR and other compliance laws
- Loss of customer trust and business revenue
- Costly emergency IT incident response
A single breach can cost a Stockholm SME more than years of preventative security investment.
How Attackers Exploit Weak Networks
Poorly secured WiFi networks serve as gateways for unauthorised access and data breaches. Attackers use several proven tactics:
Common attack vectors:
- Credential capture – Monitoring unencrypted traffic to steal usernames and passwords
- Man-in-the-middle attacks – Intercepting communications between devices and servers
- Malware distribution – Injecting malicious software into network traffic
- Lateral movement – Using initial network access to reach sensitive systems
- Ransomware deployment – Encrypting files and demanding payment for recovery
Attackers don’t need technical genius—they use automated tools that work against thousands of networks simultaneously.
Practical Security Solutions
Implementing strong encryption and authentication significantly reduces security risks. These preventative measures stop most attacks before they gain traction.
Essential solutions:
- Deploy WPA3 encryption – Make captured data unreadable to attackers
- Change default passwords – Eliminate the easiest access point
- Enable firmware updates – Patch known vulnerabilities automatically
- Segment networks – Isolate sensitive systems from guest and general traffic
- Restrict device access – Only allow approved devices on the network
- Monitor traffic continuously – Detect suspicious activity in real time
- Educate users – Train employees on phishing and social engineering risks
Network segmentation is one of the most effective defences. If attackers breach your guest network, they cannot reach your financial systems.
Why Ubiquiti Unifi Solves This Problem
Unifi’s centralised management makes security implementation straightforward. Rather than configuring each device individually, you set policies once and deploy them everywhere.
Unifi specifically addresses:
- Centralised encryption enforcement across all access points
- Automatic firewall rule deployment to all gateways
- Real-time traffic monitoring and threat alerts
- Detailed audit logging for compliance requirements
- Easy network segmentation using VLANs
Businesses implementing Unifi security report dramatically reduced breach risk compared to fragmented security approaches.
Pro tip: Schedule a security audit today focusing on your current encryption standard, firmware versions, and whether you’re segmenting employee, guest, and IoT traffic. Most SMEs discover they’re running outdated encryption or have never separated network traffic—fixing these two issues alone blocks the vast majority of common attacks.
Strengthen Your SME Network with Professional Ubiquiti Unifi Solutions
Securing your wireless network is essential for protecting sensitive business data and ensuring seamless connectivity. At natverkstekniker.se, we understand the challenges outlined in the article around outdated encryption standards and fragmented network management. Our expertise in professional installation and comprehensive configuration of Ubiquiti Unifi systems equips your business with a reliable, future-proof network that embraces WPA3 security protocols, VLAN segmentation and centralised management.
Do not let poor WiFi security or substandard cabling compromise your operations. Benefit from expert network cabling using Cat6A and Cat7 that ensures optimal speed and durability. To safeguard your network and maximise performance, Boka Tid with our certified specialists today. Call us at tel:0840011726 or send an email to kontakt@natverkstekniker.se for prompt assistance. Discover how our tailored Ubiquiti Unifi installations and structured cabling can transform your SME network into a secure, efficient asset. Visit natverkstekniker.se to learn more and take the first step towards enhanced network security and stability.
Frequently Asked Questions
What does secure WiFi mean for SMEs?
Secure WiFi involves protecting all components of your wireless network, including access points, switches, and client devices, through active management and appropriate configuration.
How can I improve the security of my wireless network?
To enhance your network security, use current encryption standards like WPA3, keep firmware updated, implement strong authentication, segment your network, and continuously monitor for threats.
What are the risks of using outdated WiFi protocols like WEP or WPA?
Outdated protocols like WEP are easily hacked, while WPA is still vulnerable to several attacks. Using modern protocols like WPA2 or WPA3 significantly improves security against potential breaches.
Why is professional installation important for my WiFi network?
Professional installation ensures optimal network performance and reliability, helping to reduce downtime, prevent interference, and ensure compliance with standards, ultimately extending the lifespan of your network infrastructure.